DataStealth secures sensitive information no matter how it moves, through APIs, jobs, databases, or legacy file transfers. That means you don’t need to rewrite applications or re-architect integrations.
schedule a demoFrom legacy FTP jobs to modern APIs and streaming data, DataStealth safeguards sensitive information everywhere it moves – applying tokenization, masking, or encryption at the protocol layer before data reaches its destination.
HTTP / HTTPS (Inline, API)
Echoback Service API
-
-
-
-
SSH / SFTP / SCP
FTP / FTPS
-
-
-
-
SMTP
TCP
-
-
-
-
MSSQLServer
Oracle
PostgreSQL
DB2
SAP-HANA
SAP-DIAG
Works with the protocols your systems already use – from legacy databases to modern microservices.
No need for custom connectors or middleware rewrites – DataStealth deploys as an inline gateway or proxy.

Book a session to see how DataStealth secures your workflows.
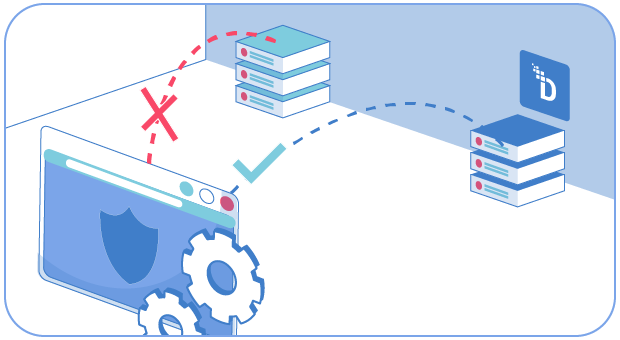
Get a sessionProtocol-level data protection intercepts and secures sensitive data as it moves through standard communication protocols – i.e., HTTP/HTTPS for web and API traffic, SQL/NoSQL wire protocols for database queries, SFTP/FTP for file transfers, and SMTP for email.
Rather than requiring each application to implement its own security logic, DataStealth sits inline at the protocol handler layer – inspecting traffic, identifying sensitive fields through real-time classification, and applying tokenization, masking, or encryption before data reaches its destination.
This is the core of a data-centric security architecture – protection travels with the data across every protocol, rather than depending on perimeter controls that fail the moment an attacker breaches the network.
Many enterprises still depend on FTP, FTPS, SFTP, and SCP for batch jobs, partner data exchanges, and mainframe-to-cloud pipelines. These protocols were designed for reliability – not for field-level data security.
DataStealth intercepts file transfer traffic at the protocol layer, discovers and classifies sensitive content within the payloads being transferred – e.g., CSV exports containing cardholder data or PDF reports with patient records – and applies protection before the file lands at its destination.
The result is that file shares and partner endpoints only ever receive de-sensitized data. No changes to existing transfer scripts, no new middleware, and no disruption to batch schedules.
Yes. DataStealth deploys as a database proxy – sitting between applications and the database engine (SQL Server, Oracle, PostgreSQL, DB2, SAP HANA) to enforce field-level tokenization or masking on queries and result sets.
Applications send standard SQL as usual. DataStealth inspects the traffic, applies configured protection policies to sensitive columns – e.g., tokenizing credit card numbers, masking Social Security Numbers – and returns protected values to the application.
Because tokens preserve the original format and length, existing joins, analytics, and reporting continue working without code changes.
This approach is particularly valuable for PCI DSS and HIPAA compliance – databases that only store tokens or masked values fall outside of audit scope entirely, reducing both compliance cost and breach exposure.
DataStealth protects HTTP/HTTPS traffic inline – inspecting REST, gRPC, GraphQL, and SOAP payloads as they pass through API gateways, service meshes, or reverse proxies. Sensitive fields within JSON, XML, and HTML bodies are tokenized or encrypted before reaching backend services or SaaS applications.
For API tokenization use cases – e.g., protecting cardholder data in payment API calls or masking PII in customer-facing endpoints – DataStealth ensures that sensitive data in transit never reaches downstream consumers in cleartext.
The platform deploys across on-premise, cloud, and hybrid environments, applying the same protocol-level policies consistently regardless of where the API traffic originates. For best practices on securing API layers, read API Security Best Practices.