Eliminate processor lock-in, slash PCI costs, and neutralize breach impact with one unified, agentless data security platform.
Schedule a DemoYour most valuable data (e.g., passenger manifests, loyalty profiles, and millions of daily transactions) flows across booking engines, payment processors, and fraud platforms. This fragmentation creates unavoidable financial, regulatory, and security risk.
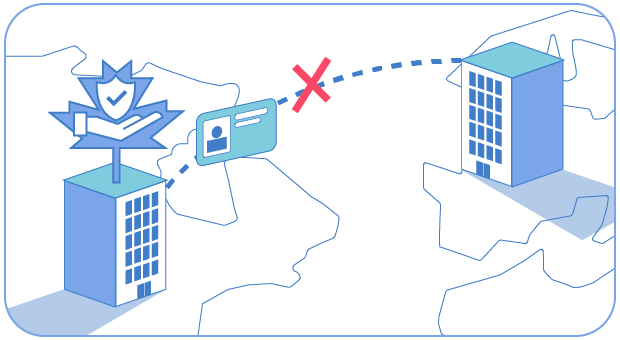
Hard-coded processor integrations trap you into one provider. When fees spike, your only choice is to absorb the hit or face crippling break fees.
Thousands of card transactions a day create an enormous CDE. Audits, remediation, and compliance costs never stop draining resources.
PII and payment data are scattered across GDS feeds, booking platforms, and third-party fraud tools – impossible to secure consistently.
DataStealth sits invisibly in your network, enforcing a single data protection policy across every system, partner, and app – without touching your code.

Independent vaulted tokenization makes processors interchangeable. Regain control, cut fees, and switch providers without disruption.
By removing PANs before they enter your systems, PCI audit scope collapses – reducing cost and risk at the same time.

Apply the same controls across booking engines, SaaS platforms, and GDS partners. Guest PII is secured everywhere it flows.

A major travel provider was hit with a 400% jump in processor fees, with millions in costs or break fees looming.
DataStealth’s vaulted tokenization meant they – not the processor – owned their data, making provider changes seamless.
They switched vendors with zero disruption, avoided break fees, and cut processing costs by 20%, saving millions annually.
Treat processors as services, not dependencies. Gain agility for M&A, new partners, or fee negotiations.
Protect PNRs, passports, and guest PII across GDS feeds, booking engines, and databases.
Share data safely with airlines, hotels, and fraud vendors using inline masking and conditional access.
Localize sensitive data to specific jurisdictions to meet residency and privacy rules.

Proven, horizontally scalable tokenization supports peak-season transaction volumes with no latency.
This isn’t a demo. It’s a working session with a DataStealth architect.
Walk away with a clear, technically viable plan to secure your most critical data while cutting costs and complexity.
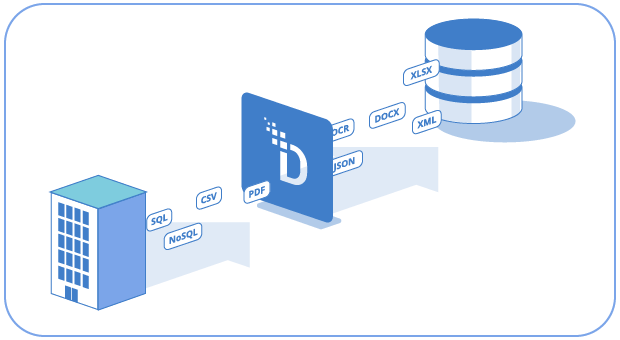
Traditional payment architectures embed the processor's tokenization directly into your systems – i.e., the processor generates and manages the tokens, which means your cardholder data is only accessible through that specific processor. If you want to switch vendors, you face migration costs, break fees, and the risk of data loss.
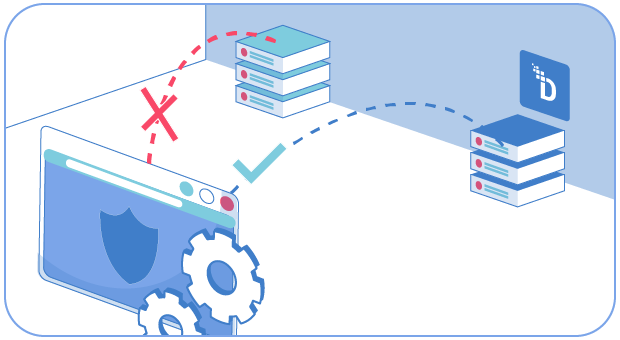
Independent vaulted tokenization puts the token vault under your control. DataStealth intercepts cardholder data at the protocol layer and replaces PANs with your tokens before data reaches the processor. The processor receives tokens, processes them, and returns results – but never touches your real cardholder data.
When you need to switch processors – whether for better rates, M&A consolidation, or geographic expansion – the transition is seamless.
Your token vault stays intact, your tokens don't change, and no cardholder data needs to be migrated. A major travel provider saved millions using exactly this approach – turning a 400% fee increase into an opportunity to cut costs by 20%.
Travel companies process millions of card transactions daily across booking engines, POS systems, loyalty platforms, and partner integrations.
Under PCI DSS, every system that touches cardholder data falls within the CDE – and every CDE system requires assessment, remediation, and ongoing monitoring.
DataStealth tokenizes PANs in-flight before they enter downstream systems. Since tokens are not cardholder data, the systems that process them are excluded from PCI scope.
For a travel company with hundreds of interconnected systems, this can mean up to 90% scope reduction – translating directly into fewer systems to audit, lower QSA fees, and faster certification cycles.
The cost impact is substantial. Large travel enterprises spend millions annually on PCI compliance – assessment fees, penetration testing, remediation, and staff time.
Reducing scope by 90% doesn't just reduce cost – it frees those resources for revenue-generating initiatives like new booking channels, loyalty features, and partner integrations.
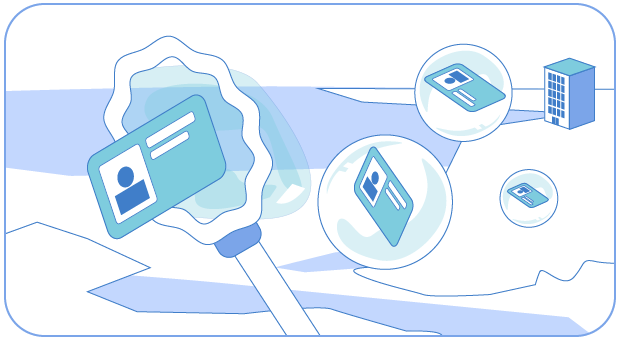
Passenger data flows through a uniquely fragmented ecosystem – GDS providers (Amadeus, Sabre, Travelport), booking engines, airline and hotel systems, SaaS fraud platforms, and dozens of partner integrations. Each touchpoint creates another copy of PNR data, passport numbers, and payment details.
DataStealth intercepts this data at the network layer – tokenizing sensitive fields before they leave your environment. Partner systems, GDS feeds, and SaaS applications receive format-preserving tokens that work in their systems but contain no exploitable PII.
For internal workflows – e.g., customer support, revenue management, analytics – dynamic masking ensures each user sees only the fields their role requires.
A gate agent sees the passenger name and seat assignment; a revenue analyst sees aggregate booking patterns without any PII. This eliminates the data sprawl problem that makes travel ecosystems so difficult to secure.
Travel companies operate across dozens of jurisdictions simultaneously – EU passengers are protected by GDPR, Canadian passengers by PIPEDA, and each market may have additional local privacy requirements. Booking data, loyalty records, and payment information must comply with the residency rules of each passenger's home jurisdiction.
DataStealth enforces residency at the data layer. When passenger data needs to flow to a SaaS platform or partner system in another jurisdiction, DataStealth intercepts the flow and replaces PII with tokens before it crosses the border. The receiving system processes tokens – not personal data – so the transfer falls outside the scope of most residency regulations.
For travel companies running hybrid or multi-cloud architectures across regions, the same policy framework enforces residency rules consistently regardless of the underlying infrastructure. Compliance is architectural, not contractual – eliminating reliance on vendor DPAs that can be invalidated by a single court ruling.